Using IAM role
Using IAM role
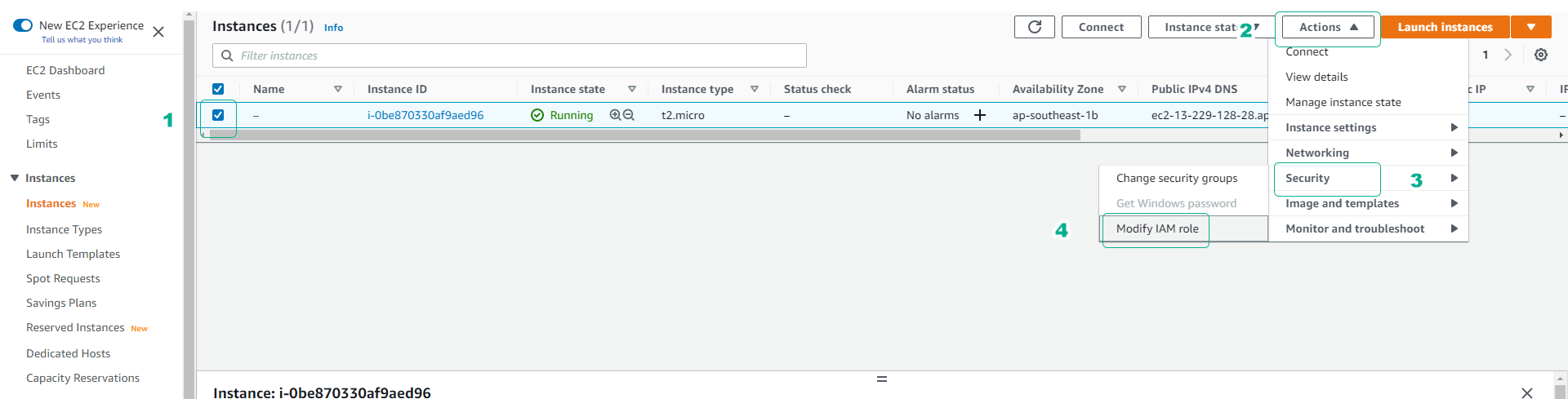
- Go to EC2 admin interface
- Click on the EC2 instance we created.
- Click Actions.
- Click Security.
- Click Modify IAM role.
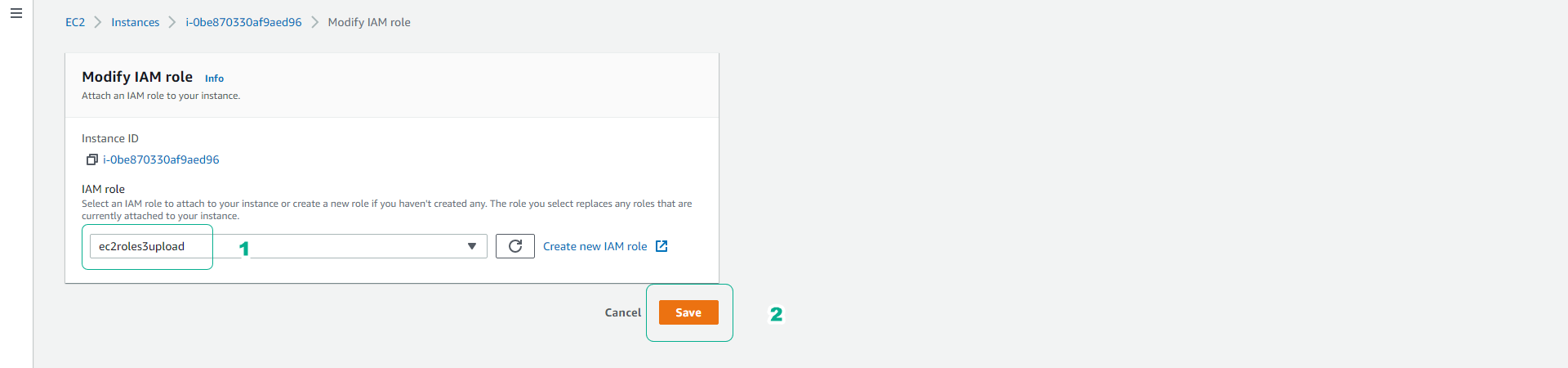
- Click the role ec2roles3upload.
- Click Save.
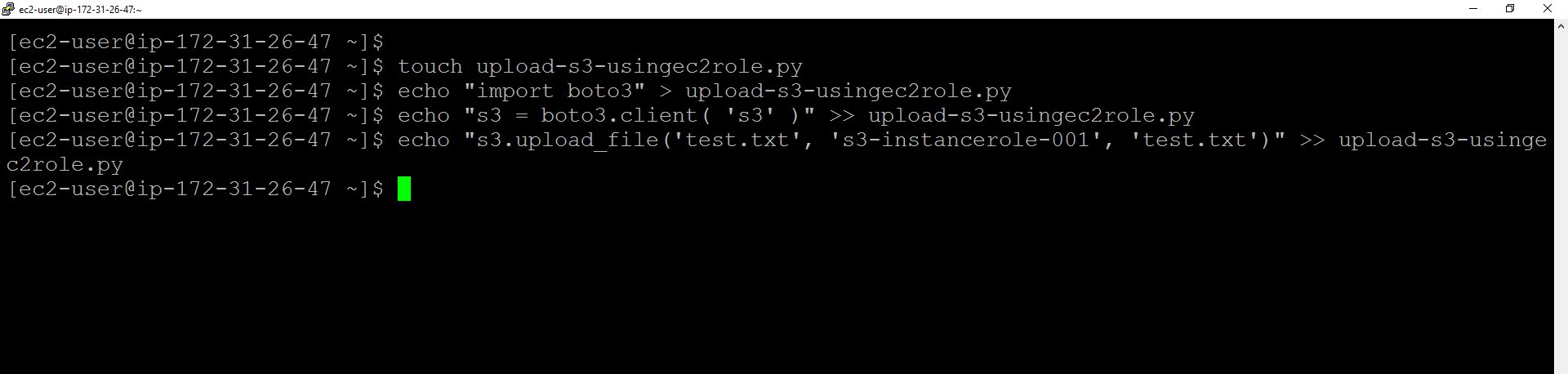
- Return to the command line interface of the EC2 instance.
- Run the following command to create a python application file.
- Note that the value should match your value.
touch upload-s3-usingec2role.py
echo "import boto3" > upload-s3-usingec2role.py
echo "s3 = boto3.client( 's3' )" >> upload-s3-usingec2role.py
echo "s3.upload_file('test.txt', '<S3BUCKETNAME>', 'test.txt')" >> upload-s3-usingec2role.py
- Let’s run our python application to upload files to the S3 bucket.
python upload-s3-usingec2role.py
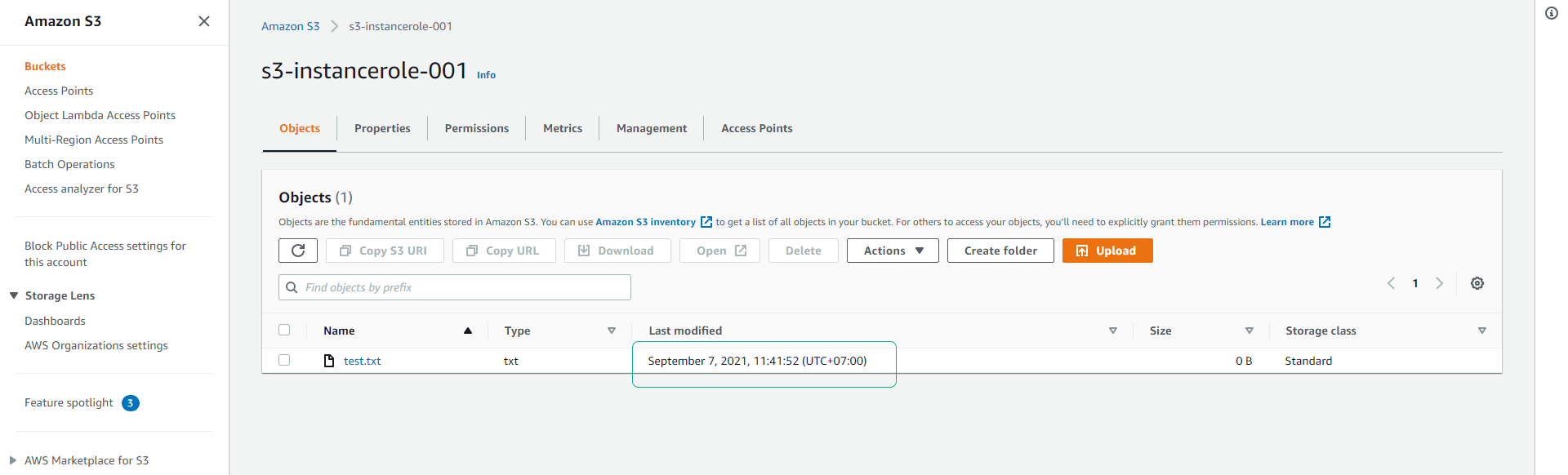
- Access the S3 service interface.
- Click S3 bucket s3-instancerole-001.
- Check that the file has been successfully uploaded to the S3 bucket.
When using an IAM role assigned to an EC2 instance (also known as an EC2 instance profile). The application on the EC2 server retrieves the security credentials provided by the IAM Role from the EC2 metadata iam/ security-credentials/role -name. The application is authorized for the actions and resources that we have defined for the IAM role through the security credentials associated with the IAM role.
We can check the security credentials generated for the IAM role ec2roles3upload with the following command. We can see that the credentials have an expiration time ( Expiration ) and will be automatically refreshed after this expiration period.
curl http://169.254.169.254/latest/meta-data/iam/security-credentials/ec2roles3upload
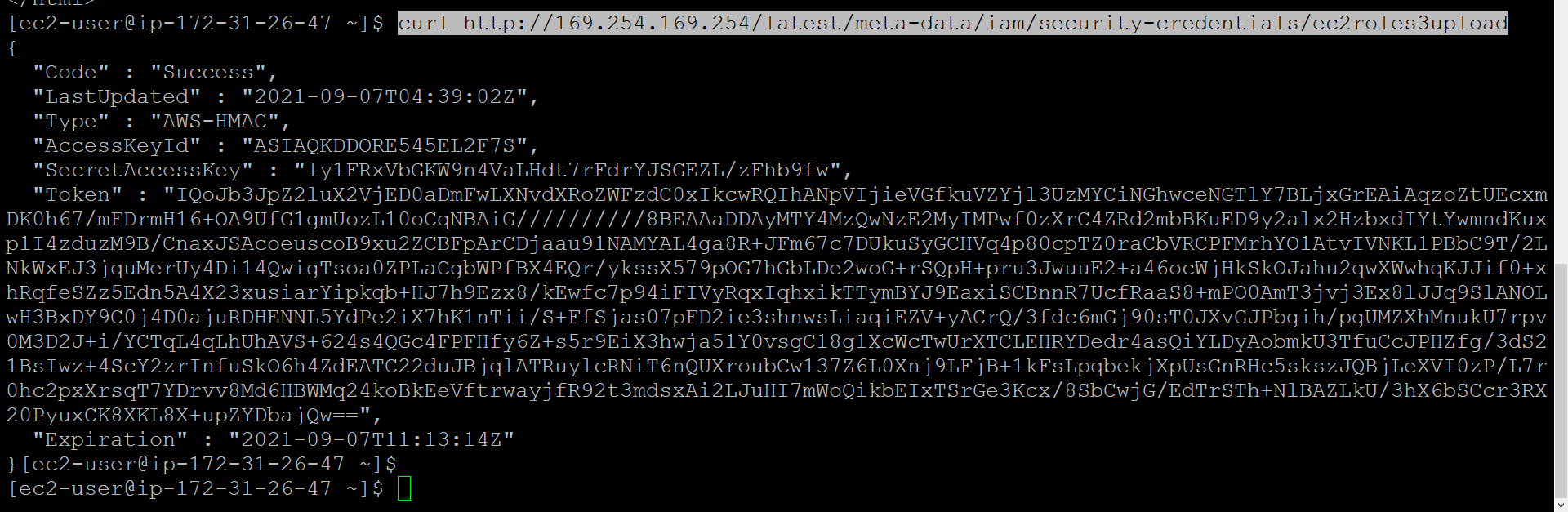
When we assign an EC2 role to an EC2 instance, the generation of temporary credentials is automatically done for us through a service called Security Token Service ( STS ). We can also use the AWS CLI in an EC2 instance that has been assigned the IAM role without any configuration. ( aws configure )
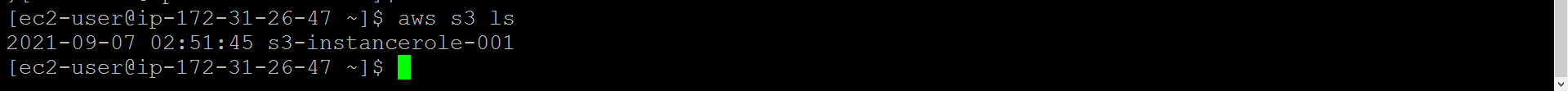
Run the following command to list the S3 bucket in the account:
aws s3 ls